Integrating Azure AD SSO with Axis LMS

If you use Azure AD as your SAML identity provider (IdP), you can use the information in this document to set up SAML authentication for your Axis LMS.
These steps assume that you have permissions for modifying your organization’s Azure AD portal.
Note: These steps reflect a third-party application and are subject to change without our knowledge. However, even if the steps described here do not fully match the screens you see in your IdP account, using these steps along with the IdP’s documentation should still enable you to configure the integration.
Step One: Begin Adding The Integration In Axis LMS
- While signed in to Axis LMS as an administrator, go to System > Integration > Single Sign-On (SSO) > SAML Sign-In
- Click the + Add An Integration button.
- Select Azure AD from the list of SAML Identity provider.
- Keep this screen/tab open for now as we will refer to it later.
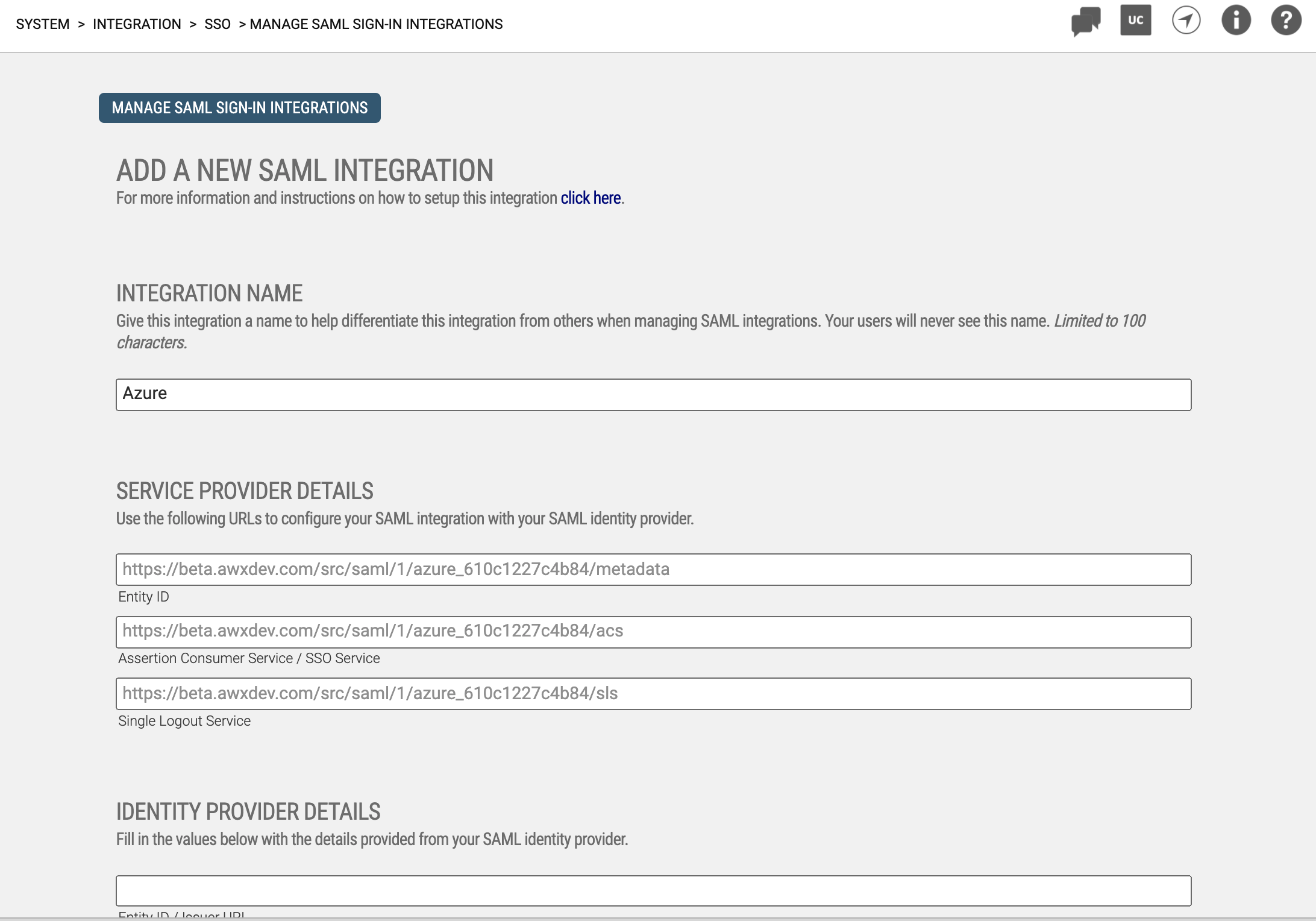
- Figure 1: Add A New Integration Screen in Axis LMS
Step Two: Adding Axis LMS To Your Azure AD Applications
- In a new tab/window, access Azure AD.
- Go to Enterprise Applications > New Application.
- Search for Azure AD SAML Toolkit
- Select the Azure AD SAML Toolkit app
- Edit the Name, entering Axis LMS.
- Click Create.
- You'll be automatically forwarded to the manage application screen for your new application. Leave this open for now as you'll refer to it later.
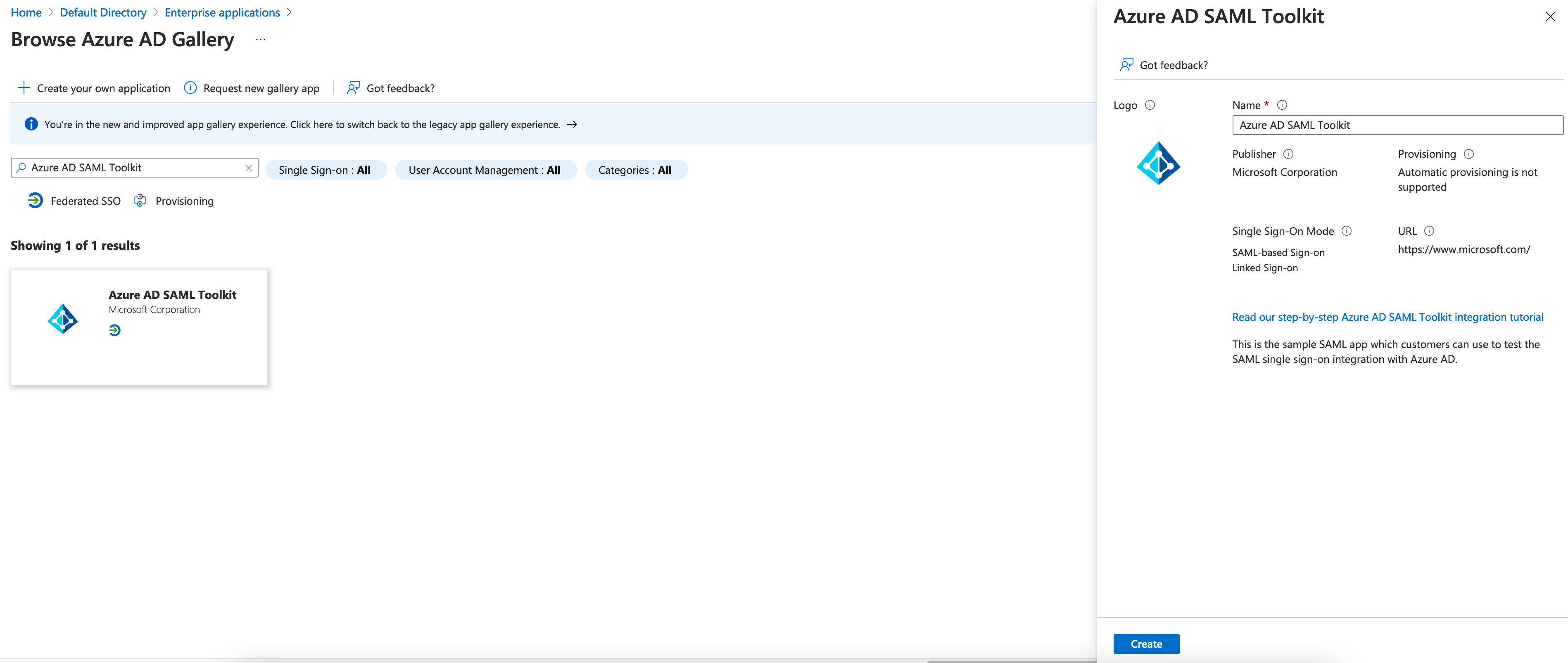
- Figure 2: Azure AD > Find Applications
Step Three: Add Identity Provider Details To Axis LMS
In this step, you'll provide Axis LMS with the SAML Identity provider values it needs to communicate with Azure AD.
- the Azure AD manage app UI, select the Single Sign-On tab.
- Click the option for SAML.
- On the SAML Setup screen, scroll down to the fourth section, titled Setup App Name.
- Copy values from Azure AD and paste them into the Identity Provider Details section of Axis LMS, as shown below.
| Copy Azure AD Field Value | to | Axis LMS Field Value |
|---|---|---|
| Azure AD Identifier | to | Entity ID / Issuer URL |
| Login URL | to | SAML 2.0 Endpoint / SSO URL |
| Logout URL | to | SLO Endpoint / Logout URL |
| SAML Signing Certificate > Certificate (Base64) > Download (& open in text editor) | to | X.509 Certificate |
After copying values from the SSO tab into the Identity Provider Details section of Axis LMS, it should look something like this:
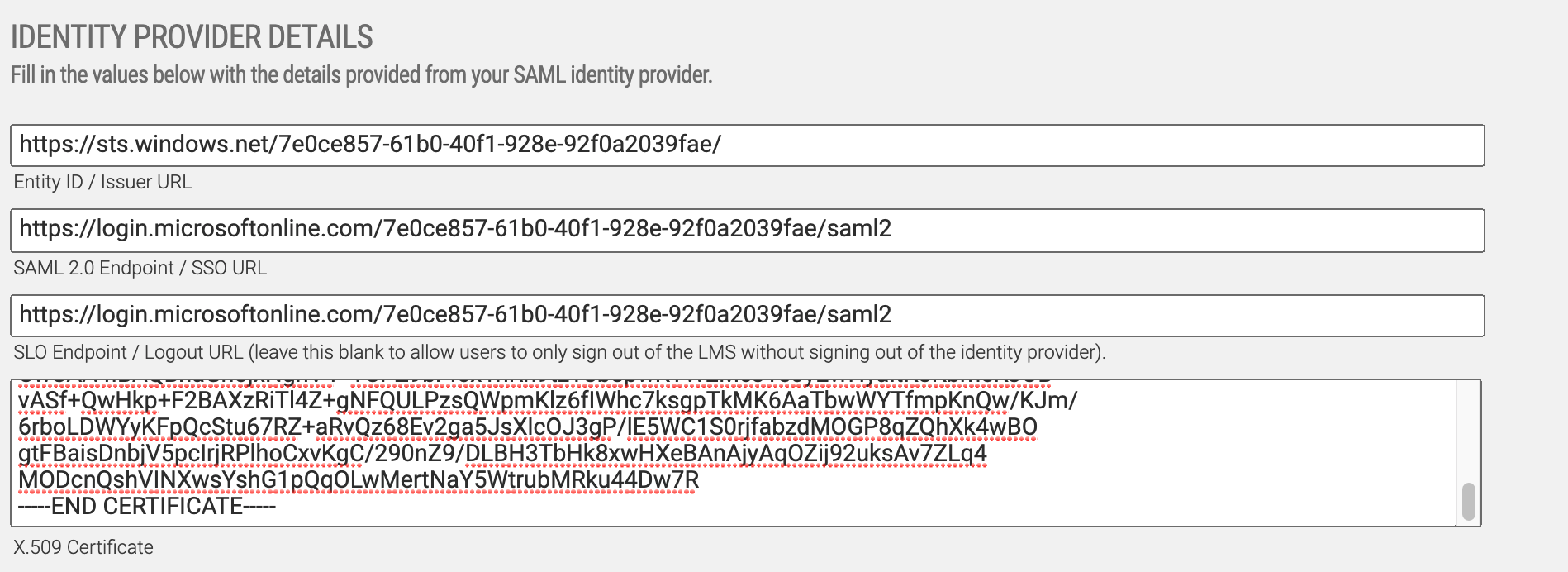
- Figure 3: Axis LMS Identity Provider Details
Step Four: Add Service Provider Details To Azure AD
In this step, we’ll define the service provider values that Azure AD will need to identify your app.
- On the Add A New Integration screen in Axis LMS, go to the Service Provider Details section.
- In the Azure AD SAML setup UI, scroll up to the Basic SAML Configuration section and click Edit.
- Copy values from Axis LMS into the Azure AD fields as shown below.
- Click Save.
| Copy Axis LMS Field Value | to | Azure AD Field |
|---|---|---|
| Entity ID | to | Identifier (Entity ID) |
| Assertion Consumer Service / SSO Service | to | Reply URL (Assertion Consumer Service URL) |
| Assertion Consumer Service / SSO Service | to | Sign On URL (* remove '/acs' from the end of this URL) |
| Single Logout Service | to | Logout URL |
In this step, we’ll define the information about the user (id, email address, first name, last name) that need to be passed to Axis LMS.
- In the Azure AD SAML setup UI, scroll up to the User Attributes & Claims section and click Edit.
- Click the Add a New Claim link in the upper left corner of the parameter listing.
- Under Name enter "uuid" (without quotations).
- Under Source Attribute, select user.userprincipalname and then click Save
- Repeat this sequence three more times, using the fields/values below
| Field | to | Value |
|---|---|---|
| emailAddress | to | user.mail |
| firstName | to | user.givenname |
| lastName | to | user.surname |
At this point you've completed all the necessary steps to configure the Axis LMS application in Azure AD.
In Axis LMS, on the Add A New Integration screen, finish configuring the User Login settings and then click Save to save the integration in Axis LMS.
To test your new integration, you'll need to give users access to your new application in Azure AD before using the newly generated Axis LMS login link for this integration. For more information on granting users access to your application via Azure AD, please refer to the IdP's documentation.